Decrypt GandCrab Ransomware. How to Recover GandCrab Encrypted Files
UPDATE: Most versions of GandCrab Ransomware can be decrypted with free tools. Please click the below button to visit our partners at No More Ransom to download the version you need!
GandCrab ransomware was first observed in January of 2018. Since then, the GandCrab has completed 5 major version releases and several minor version updates. The majority of the new versions were in response to free decryption tools released by firms such as Bitdefender, For every free decryption tool released, the GandCrab developers quickly responded with a new version. GandCrab is relatively unique in its distribution tactics and serves as a benchmark for how Ransomware-as-a-Service is operated. The operators behind the GandCrab payment TOR site provide support to distributors that purchase a GandCrab kit and lay the attacks. Given GandCrab’s prevalence, it’s important to understand how a GandCrab ransomware attack occurs and the steps that must be followed if a victim needs to pay the ransom and run the decryption tool.
How Do GandCrab Attacks Happen?
GandCrab Ransomware attacks happen in a myriad of ways. Because the ransomware kit is so actively syndicated, the attack vectors vary and change frequently. Remote Desktop Protocol continues to be a common attack vector for GandCrab. This is due to the prevalence of poorly secured RDP ports and ease of access through brute force or purchasing credentials on dark market sites. Companies that allow remote access without taking the proper protections are at grave risk of being attacked by GandCrab Ransomware. Email phishing is also increasingly prevalent in GandCrab attacks. Exploit kits such as Trickbot, Mimikatze or Emotet are increasingly used by attackers to procure elevated credentials which allow them to encrypt the entire network of a targeted organization. GandCrab distributors are also known to exploit unpatched CVEs that allow remote code execution.
How Does GandCrab Encrypt Files?
Once GandGrab is installed, the malware first kills processes that may impede the encryption process. It also checks the keyboard layout and if it detects a Russian keyboard, stops its process. During encryption, GandCrab uses a Tiny Encryption Algorithm (TEA), a lightweight and hard-to-detect process to encrypt files on an affected machine. GandCrab also uses a specific random algorithm to generate URLs for each ID it creates. This ID is used as the encrypted file extension and is dropped onto a ransom note as well on the impacted machine. A corresponding TOR site is created for each of these IDs.
How Do You Identify If GandCrab Has Encrypted Your Files?
GandCrab Ransomware appends a random string of letters to each encrypted file. It also generates a ransom note that is titled with the encrypted extension +manual.txt.
An encrypted file would follow the below pattern (example of a word document):
Filename.doc.ABCDEF
The corresponding ransomware note would be titled ABCDEF-manual.txt. This full MUST not be removed from an encrypted machine as the key within the file is necessary for decryption to run. AV software that may delete or modify this file should not be run if there is a risk of deleting or destroying it. An example of a typical GandCrab ransom note is below:
Components of a GandCrab Ransom Note
Version of GandCrab Ransomware
In the top left corner of the ransom note, the version of GandCrab Ransomware is specified. It is important for victims to identify this version before taking any recovery steps as several versions of GandCrab have free decryption tools available. It is also not uncommon for distributors to use decryptable versions of Gandcrab for some time after the tool has been released.
Visiting the GandCrab TOR Site
After commenting on the encrypted nature of the files, the note instructs the victim on how to download the TOR browser and visit the unique TOR site the corresponds to the ransom note and ID.
Leave the Ransom Note in Its Location
The key listed at the bottom of the note is necessary in order for the decryption of the corresponding encrypted files to take place. As instructed, it is important that victims do not move or delete these ransom notes, as the GandCrab decryptor will look for them during the decryption process. If they are deleted, the decryption will not be possible.
How to Decrypt GandCrab Ransomware Encrypted Files?
The GandCrab TOR site is relatively straightforward for victims to navigate. If you would like an in-depth review of the TOR sites features, please see our prior guide. Be leery of any company that claims to be able to decrypt current versions of GandCrab using proprietary methods. Also check the version to see if a free decryption tool is available before contemplating whether or not to pay.
If you needed to pay the ransom, you will need to wait for 3 blockchain confirms before the TOR site will reveal a link to download the decryptor. Victims that choose to negotiate for multiple IDs via chat can also receive batches of decryptors directly via the chat box.
Check for Free Public GandCrab Decryptors
Just to reiterate, previous versions of GandCrab have been decrypted by the IT security community and shared with the public. If the version of GandCrab that encrypted your files is older, then you may be in luck. Head over to No More Ransom to see if a decryption tool is available. If you don’t see one, read below to continue your ransomware recovery.
GandCrab Decryption Instructions from the TOR Site
Victims of GandCrab ransomware should consider making a 1x1 copy of all encrypted files prior to starting the decryption process. Please follow this guide for a more detailed plan on how to safely make copies of encrypted data. Additionally, be sure you have adequate disk space to run decryption. You will need twice the disk space of the encrypted files to run the decryptor (to decrypt 100gb of files, you need 100gb of free space). If you don't have sufficient disk space, move the encrypted files to a place that does (be sure to move the -manual.txt files as well). As the decryptor runs, it will create a copy of each encrypted file and decrypt the copy, not the original file.
The Instructions provided on the TOR site are rudimentary but do a decent job explaining how the decryptor runs. The steps are:
1. Open machine as administrator;
2. Disable your Anti-Virus (it will interfere with the tool);
3. Be sure the -manual.txt file stays with the encrypted files. The decryptor tool won't run if that .txt file is not on the machine;
4. Download the decryptor tool;
5. Run decryptor.exe as administrator.
GandCrab Decryptor Options
There are two command line options available for users who want to use the console (cmd.exe) to run the decryptor. These options allow the user to either point the decryptor to a specific path (vs decrypting all mapped drives) or run the decryptor without having it automatically create a copy. Options can be used together.
To specify a decryption path: you can specify a target file or a folder to decrypt. For example:
cmd.exe C:\Users\Username\Desktop\Decryptor_5.[x].exe -path E:\some_folder\
No copies: if you absolutely need the decryptor to run faster and have already created backups of your encrypted data, you can run ‘noback.’ In this mode, the decryptor will work without creating a copy. It is a lot more risky and can damage or permanently lose data if the decryption is not successful as no backup is created. We strongly recommend NOT using this option.
How to Use The GandCrab Decryptor Tool
The decryptor will be provided in a .zip folder. Open the file and then open the .exe provided (ensure you have the file storage per above). The file will look like the below:
What the GandCrab Decryptor .exe looks like when first downloaded from the TOR site.
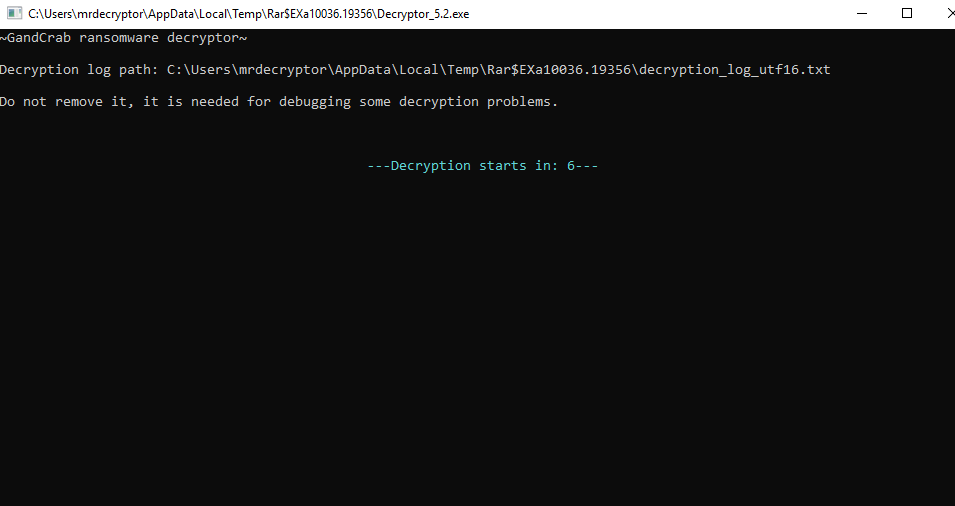
2. When you open the decryptor executable, it will open an application that looks like the below with a countdown before it begins the decryption process.
The application window of the GandCrab Decryptor before it starts
3. While the decryptor is running, the application will look like the below. It will show a file count, and a success / failed file count in the upper right corner.
The application window of the GandCrab Decryptor as it scans and decrypts
4. When the decryptor completes, you will get a success metric pop up like below.
The application window of the GandCrab Decryptor once it completes
Troubleshooting the GandCrab Decryptor
When you run the decryptor, it will create a log file called: decryption_log_utf16.txt. This file is created in the same directory as the decryptor. The log file has errors identified by "error codes". These codes write to the log file after every file procedure. There is a list of several common errors:
0x5: this error usually means that the decryptor does not have enough rights. You should run decryptor as administrator to avoid this error.
0x3, 0x27, 0x70: most of the time, this means that the decryptor isn't able to create a copy of the file. First of all, make sure you have enough space to create a backup file.
If you are experiencing a ransomware incident involving GandCrab or any other variant, please don’t hesitate to reach out for help.